Lessons Learned on an Introvert’s Journey to Leadership
Category:EDUCAUSE,Introverted Leadership,introverts,Leadership,Lessons Learned Note: This article was previously published on October 17, 2016 in the EDUCAUSE Review The Professional Commons Blog.
Note: This article was previously published on October 17, 2016 in the EDUCAUSE Review The Professional Commons Blog.
Many of us might agree that Western society lauds extroverted leaders and their accomplishments. However, introverts make great contributions and can be effective leaders too. As IT professionals, many of you are introverts, and you certainly work with a lot of introverts. Those of us who are introverts may not believe or recognize that we have strong leadership skills, and we certainly don’t seem like the extroverted leaders that are the norm in Western society.
I’m an introverted leader, despite outward appearances. I’ve presented at conferences numerous times, and overall, I’m able to mix well in business settings. Many people who see me in that very public context are surprised that I’m an introvert. My introversion informs my approach to leadership, and I’ve found that self-understanding has helped me learn how to harness my strengths as an introvert to become an influential leader and to achieve great results.
I thought it might be helpful to share a bit of my journey to leadership, to talk about what’s worked for me, and to provide strategies for both discovering your introvert strengths and maximizing them in your workplaces.
First Things First: What’s an Introvert?
Please regard this section as a generalization constructed from a number of sources. Introversion and extroversion lie along a spectrum. Individuals may be more or less extroverted or introverted. It’s also important to note that social anxiety or fear of public speaking does not necessarily mean that someone is introverted. (Many articles and discussions state that public speaking is the number-one fear for most people.)
For the purposes of this blog post, I’ll characterize extroverts and introverts as follows:
- Extroverts focus on the outer world of people and things. They tend to be active and have a wide breadth of interests. They understand things through experience. They may be reward seekers and desire fame. They are energized by contact and activities undertaken with others.
- Introverts have a rich inward-looking life of ideas. They tend to have a depth of interest, preferring specialization to a breadth of knowledge. They may mull over thoughts and concepts, but not express those thoughts verbally or externally. Introverts recharge themselves by withdrawing from the hubbub to places of quiet and solitude.
Reading these descriptions, can you see where you might fit on the spectrum?
Applying Introverted Strengths to Leadership
There are many approaches to leadership, and we often hear about highly extroverted, “take charge” leaders who have very public presences. However, as Susan Cain and others have pointed out, there’s no correlation between success in leadership and extroversion. Examples of introverted leaders include Albert Einstein, Steve Wozniak, and Abraham Lincoln. What made them good leaders? In what ways were they influential?
- Einstein was known for his depth and clarity of thought (and his genius). He had the ability to look at all angles to a problem and develop innovative (and often unexpected) solutions.
- Wozniak was responsible for many of Apple’s innovations, even though Steve Jobs was the best-known leader and public spokesperson for Apple. Working outside the limelight, Wozniak was able to engineer technological breakthroughs. Together, Jobs and Wozniak arguably revolutionized the end-user computing experience.
- Lincoln was not gregarious and certainly not known as a compelling public speaker. Yet he was a deep strategic thinker and provided leadership during what may have been the most trying times for the United States.
All were introverted leaders, and all were very effective.
My Background
I’ve had a career that spans many disciplines, including a stint as a doctoral student in early modern European history, a technical communicator, and an information security practitioner. (I took a rather circuitous route to my current position as program manager in the Information Security Office at the Rochester Institute of Technology.)
As a doctoral student, I tended to be very reticent in classes, not wanting to contribute to discussions in which I was sure everyone else was much more knowledgeable.
In my work as a technical communicator, I documented ISO 9000 processes, created hardware and software documentation, and eventually moved into a consulting position where I had responsibility for end-user communications for an IT organization in a local Fortune 500 company.
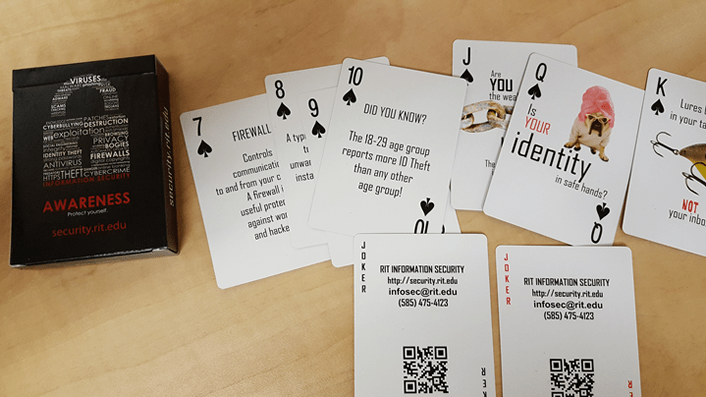
As a security awareness professional, I communicate to my campus community about information security issues and threats, develop training courses in digital self-defense, and contribute to the greater information security community through my Introverted Leadership Blog and the EDUCAUSE HEISC Awareness and Training Working Group(HEISC is the Higher Education Information Security Council).
I didn’t seek leadership positions and preferred to remain in the background. The last place I wanted to be was the center of attention with colleagues looking to me for direction. Happily, my willingness to accept volunteer tasks has enabled me to share ideas and develop my leadership abilities.
My Transformation into a Leader
Although there are many formative steps I could look back on, the steps below have probably helped me the most.
Gaining a Better Understanding of Introversion
I read Cain’s book Quiet shortly after it came out. I found her research and discussion around various facets of introversion in American culture to be compelling. Leveraging her work and other sources, I co-presented on the subject of introverted leadership at a few conferences. The topic was popular, and we had standing-room-only crowds. At that point, I realized that this subject was of great interest to my professional colleagues, both in technical communication and in information security. I was intrigued and did further research into what it meant to be an introvert who was also a leader.
Understanding My Personality/Temperament Type
There are various tools for determining your personality/temperament type and many resources discussing the leadership styles most appropriate to those types. Around the time I stepped into a leadership role, I became acquainted with the Myers-Briggs Type Indicator (MBTI) and the work of David Keirsey on temperament. I’m not going to give an in-depth description of MBTI or temperament here. In short, the MBTI and similar tests provide a series of questions; your responses group you into specific personality or temperament types: Introvert/Extravert; iNtuitive/Sensing; Thinking/Feeling; Judging/Perceiving. The types, which are identified through the four pairs, are not distributed evenly throughout the population. The results fall along a continuum, so not every INTJ will be the same. (Obviously, we’re more complex than a four-letter descriptor can convey.)
I’m an INTJ (Introverted-iNtuitive-Thinking-Judging). Keirsey describes the INTJ as a Mastermind. (Others assign the term Scientist to this combination of traits.) Finding out I was an INTJ was important to me because the description affirmed my ability to lead (albeit reluctantly), discussed my strengths and weaknesses, and provided strategies for success as a leader. I had to see something on paper stating that I could be a leader before I could accept that ability. I needed the affirmation. There are times I feel like the Scarecrow in The Wizard of Oz, needing a diploma (or confirmation in print) to prove to myself that I have a brain.
Understanding How I Communicate and Work Best
By and large, introverts are not comfortable being asked to give an immediate response to suggestions, nor do they enjoy engaging in small talk. I’m not at my best when asked to provide an on-the-spot answer to how I might handle a specific problem or an idea for the best way to move forward. However, when given time, I can respond with a well-thought-out and nuanced response. I’ve also found that I communicate best in writing, although my oral communication skills have become stronger over time and I’m now a seasoned presenter.
I prefer to work individually, and my work is not necessarily done at a steady pace. I enjoy “collisions” with other thinkers, but I prefer not to work in teams. Teams often follow leaders who express their ideas confidently and quickly, neither of which are guarantors that the ideas are actually good. Individual conversations, on the other hand, can often lead to breakthroughs and innovations.
Building on Small Successes
I’ve had many opportunities to grow in leadership, but they’ve occurred primarily outside of my professional work environment and often in nonprofit organizations, which are always looking for competent and dedicated volunteers. For me, that leadership path has been through two organizations: the Society for Technical Communication (STC), an international organization devoted to furthering technical communication and educating its members; and the EDUCAUSE HEISC. As I volunteered in STC, I was asked to serve in a variety of positions with increasing responsibilities. I was eventually elected president of the Rochester Chapter and later served on the board of directors at the international level. For HEISC, I served as co-chair of the Awareness and Training Working Group. In that role, I’ve had the opportunity to facilitate a group of talented information security professionals.
I didn’t seek leadership positions in these organizations, but for almost every opportunity presented to me, I’ve said “yes.” I’ve also asked myself: “How can I make a difference in the organization?” (Say “yes” when given an opportunity to serve. You won’t grow in leadership if you don’t take advantage of opportunities to practice leadership.)
Making It Personal: Examining My Strengths and Growth Opportunities
From my discussion above, it’s clear that self-discovery has been an important component in how I’ve learned to harness my introvert strengths and become a leader. From my readings about personality/temperament and my experience as a leader, I’ve discovered that my strengths include my ability to identify gaps, my desire to make a difference, my commitment to practicing a servant leadership model, and my drive to pursue excellence. I’m also competitive. (That competitiveness can be both a strength and a weakness. I can push myself and others toward goals. However, I also have an innate desire to win at whatever I’m engaged in.)
Self-discovery also means you uncover your weaknesses, or growth opportunities. For me, those growth opportunities include overcoming my desire to avoid conflict, pushing past my reticence to contribute in discussions, not overanalyzing opportunities or situations before moving forward, and harnessing my competitiveness.
Where Do You Go from Here?
I recommend the following activities to help you uncover and actualize your introvert strengths and become an influencer.
- Get to know yourself. Take one of the personality or temperament assessments offered at Keirsey.com, HumanMetrics, or 16 Personalities. Read Quiet and some of the other introversion resources listed below.
- Control your environment. If you’re in an open-plan office, find ways to define your personal space to increase your ability to stay focused. (See Morgan, 5 Ways, for some great ideas.)
- Communicate your value. Keep a record of your accomplishments and make sure your management understands how you communicate and work best and how you can add the most value. Take advantage of the unhurried nature of social media to leverage the playing field by using the opportunity to clearly articulate your thoughts.
- Leverage your introversion. You have tremendous abilities to provide superior solutions because, given sufficient time, you can often see all facets of a problem and devise a comprehensive solution.
- Don’t avoid networking events. You don’t have to meet and engage in small talk with everyone. Find one or two people with whom to have an in-depth conversation, and follow up later. Depth is more important than breadth.
- Recharge (in solitude) as needed!
Conclusion
By no means do I consider myself to have “arrived,” but I am surprised by how far I’ve been willing to journey in the last ten years as I’ve leveraged my introversion to lead in a way that’s natural for me. I hope the thoughts above can help stimulate your thinking about how you can leverage your introversion — and also leverage the strengths of the introverts you manage (and make them happier members of the workforce).
You’ve read a bit of my story. If you’re an introvert, what has been your experience in the workplace? If you’re an extrovert, how have you worked successfully with introverts both as their colleague and as their manager? What strategies have worked for you? Please join the conversation. I’d love to hear your stories!
Resources
Cain, Susan. Quiet: The Power of Introverts in a World That Can’t Stop Talking. New York: Crown Publishers, 2012.
Kahnweiler, Jennifer B. The Introverted Leader: Building on Your Quiet Strength. San Francisco: Berrett-Koehler Publishers, 2009.
Keirsey, David. Please Understand Me II: Temperament, Character, Intelligence. Delmar, CA: Prometheus Nemesis Book Company, 1998.
Laney, Marti Olsen. The Introvert Advantage: How to Thrive in an Extrovert World. New York: Workman Publishing Company, 2002.
Morgan, Elan. “5 Ways to Love Your Open-Plan Office.” Quiet Revolution.
Myers, Isabel Briggs, and Peter B. Myers. Gifts Differing. Palo Alto, CA: Consulting Psychologists Press, 1980.
Petrilli, Lisa. The Introvert’s Guide to Success in Business and Leadership. Chicago: C-Level Strategies, 2011.

 Think Strategically
Think Strategically